Information Security Services

Protecting Your Digital Ecosystem from Evolving Threats
Information Security Services
We offer a comprehensive suite of information security solutions designed to safeguard your applications, networks, data, and infrastructure. From proactive assessments like AS-IS Gap Analysis to specialized protections for APIs, servers, and mobile apps — our services ensure end-to-end security tailored to your business needs.
Comprehensive Information Security Services
Safeguard your digital assets with end-to-end security solutions including AS-IS gap analysis, cyber defense, application and API protection, mobile and web security, and infrastructure hardening — ensuring your business stays resilient against evolving threats.
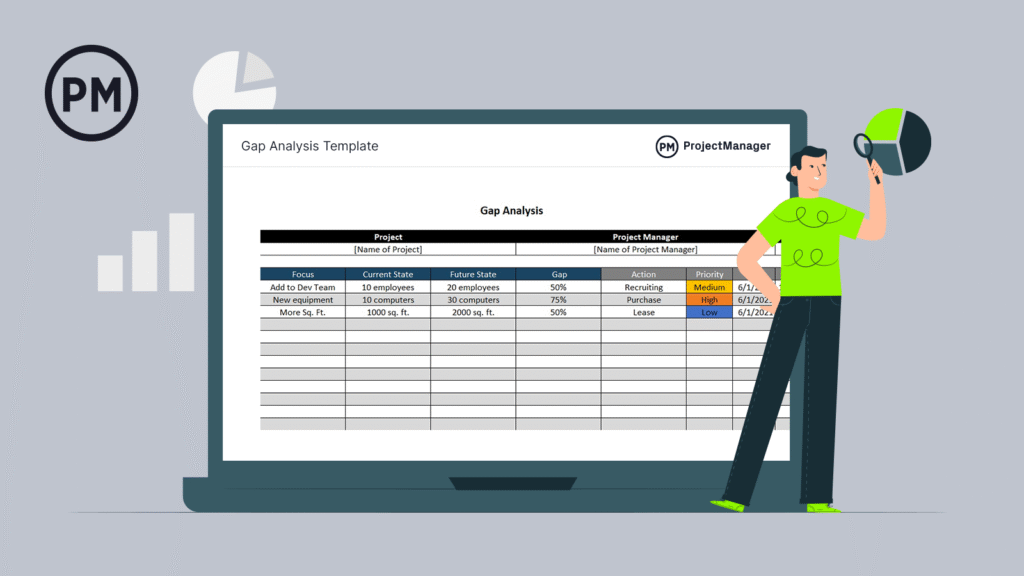
AS-IS Gap Analysis / Due Diligence
Comprehensive assessment of current security posture to identify risks, gaps, and compliance issues.

Cyber Security
Robust end-to-end protection to detect, prevent, and respond to evolving digital threats.
Application Security
End-to-end protection to identify and eliminate vulnerabilities across the entire application lifecycle.
DevSecPriOps
Seamlessly integrate security and privacy into every stage of your DevOps lifecycle for continuous, automated protection.

Web Security
Shield your web platforms from attacks with advanced protection against DDoS, XSS, SQL injection, and more.

Mobile Security
Protect mobile applications from data leaks, reverse engineering, and unauthorized access across Android and iOS.

API Security
Secure your APIs with robust authentication, authorization, and threat prevention to prevent abuse and data breaches.

Network Security
Strengthen your network with firewalls, intrusion detection, and access controls to ensure secure data flow and perimeter defense

Database Security
Protect sensitive data with encryption, activity monitoring, and strict access controls to prevent breaches and misuse.

Server Security
Ensure server integrity by hardening systems, applying patches, and monitoring for unauthorized access and threats.
